The Difference Between Computer Forensics and eDiscovery
/ GUEST BLOGGER
GUEST BLOGGER
Phillip Rodokanakis, CFE, EnCE, ACE, DFCP
U.S. Data Forensics, LLC
Herndon, Va.
In my previous posts, “Computer Forensics: Following the Digital Bread Crumbs” and “eDiscovery: Digital Data Gives Birth to New Industry”, I covered computer/digital forensics and the emergence of eDiscovery as distinct and separate professions dealing with the handling of digital evidence. Although both these disciplines deal with digital data, there is some confusion as to how they differ. Digital forensics encompasses the entire universe of data stored on a hard disk drive (HDD), whereas eDiscovery usually only focuses on a smaller grouping of data stored on the drive.
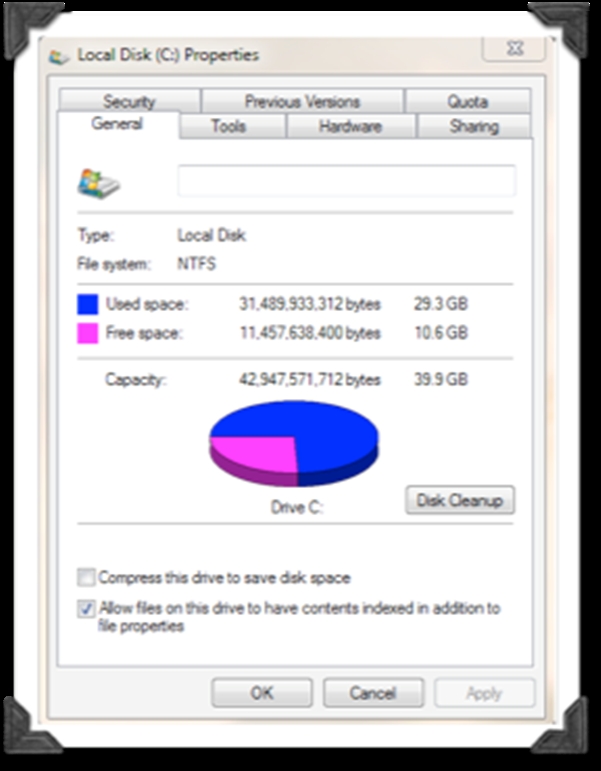
In technical lingo, the free space is referred to as “unallocated clusters” while the used space is referred to as “allocated clusters.” In computer file systems, a cluster or allocation unit is the unit of disk space allotted for files and directories.
A simple way to understand the difference between eDiscovery and computer forensics is to think of the HDD allocation model. EDiscovery focuses on data stored in allocated clusters, while computer forensics deals with both allocated and unallocated clusters (i.e., the entire physical drive).
EDiscovery filters out program, temporary and system files, and processes only active user accessible files. This usually involves Microsoft or other Office Suite files (e.g., documents, spreadsheets, presentations, databases, PDFs, etc.) and emails. These types of files are then processed in an eDiscovery engine, where they are indexed and catalogued, and then usually loaded into a Litigation Support Platform (software designed to aid law firms in the process of document reviews in litigations; for more information see the American Bar Association website).
On the other hand, computer forensics investigates everything, including deleted files or remnants from former files that have been partially overwritten. A forensic examiner must pay particular attention to certain operating system and log files, temporary files and the file remnants found in unallocated clusters.
For example, data remnants (file artifacts) from web-surfing sessions, including accessing webmail accounts (e.g., Gmail, Hotmail, etc.) and chats, are usually found in temporary Internet files or unallocated clusters. Certain system files log information pertaining to external devices, accessed files, executable software, deleted files, etc.
Certified Fraud Examiners readily recognize the critical value of digital evidence in a fraud examination. They also need to fully understand the differences in eDiscovery and digital forensics in order to be able to seek appropriate technical advice and consulting services.